Witz Cybersecurity is excited to host a SyncDog Webinar (Mobile Security) on Tuesday, 29 April 2025. This is an opportunity to learn about SyncDog’s awesome technology, which protects data on mobile devices with next-level encryption (AES 256-bit).
📅 Date: Tuesday, 29 April 2025
🕙 Time: 10:00 AM AEDT
⏲️ Duration: 40 minutes + 5 minutes Q&A
CYBERSECURITY SERVICES & TECHNOLOGIES
Solutions offered by Witz Cybersecurity
Incident Response (IR) | Posture | M&A Assessment
We partner with the global Cyber IR leader to prevent or prepare your organisation for a Cyber-attack or Cyber Breach. Cyber Posture and M&A assessments are another services we offer.
- Red Teaming
- Purple Teaming
- Tabletop Wargames
Stress-test and elevate your capabilities against real-life threats by leveraging an attacker's perspective.
Sygnia Named in the 2024 Gartner®️ Market Guide for Digital Forensics and Incident Response Retainer Services.
Autonomous Penetration Testing
Deliver autonomous pentests with cloud or hybrid infrastructures from both an internal and external attackers' perspective to rigorously test cloud security controls in the context of your entire digital infrastructure or specifically target identity-based attack surfaces in AWS or MS Azure Entra ID.
-
Internal Pentest: provide a holistic view of how attackers can chain vulnerabilities across the entire digital infrastructure, identifying complex attack paths and pivoting between on-prem and cloud environments.
-
External Pentest: This is similar to an internal test but launched from Horizon3.ai's infrastructure to validate the security of public-facing systems.
Mobile Security
Military Grade Security (AES256) protects your organisation's DATA!
- Data Encryption & Containerisation
- Security without MDM agents
- Security vs. Usability Resolution
- Zero Trust Endpoint Security
- End-to-End Data Loss Protection (DLP)
- Support for Various Industries
- Single Application Installation
- Privacy Assurance
- Compatible with Both COPE & BYOD
- Suitable for Security-Conscious Organisation
For a demo email support@witzcybersecurity.com
MXDR
Velocity MXDR is armed with comprehensive, up-to date threat intelligence, unmatched detection accuracy, and advanced forensics capabilities to neutralise threats throughout your entire infrastructure.
Sygnia’s XDR performs realtime alert processing, including enrichment, deduplication, and AI-driven forensic analysis, to provide advanced, automatic event detection, verification and filtering at scale.
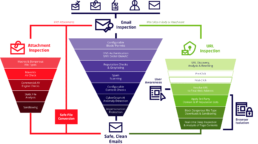
Advanced Email Security
90% of cyberattacks begin with an email. Advanced Email Security PREVENTS Spam, Phishing, BEC, Malware, Account Takeover and Zero-Day exploits BEFORE they reach organizations using Microsoft 365, Google Workspace, or any cloud and on-prem email service.
- Secure any type of email environment - M365, Google Workspace, on-premise, cloud, hybrid
- Block the most dangerous threats with AI-powered detection
- Customize policies to meet your specific needs
- Easily manage large and complex email environments
- Automate threat remediation
- Keep email flowing, no matter what
Endpoint Security
The world’s leading AI-powered platform for unified endpoint detection and response (EDR) and extended detection and response (XDR)
The AI-native CrowdStrike Falcon®️ platform combines industry-leading threat intelligence with innovative detection and response technology to better understand and stay ahead of adversaries. CrowdStrike Falcon®️ Insight XDR extends enterprise-wide visibility, detects advanced threats and responds automatically across endpoints and beyond.
Cloud Security
As a CNAPP, Orca Consolidates many point solutions in one platform, including:
- Cloud Security Posture Management (CSPM)
- Cloud Workload Protection (VWPP)
- Cloud Infrastructure Entitlement Management (CIEM)
- Vulnerability Management
- Container & Kubernetes Security
- Data Security Posture Management (DSPM)
- API Security
- Cloud Detection & Response
- Multi-cloud Compliance
- Shift Left Security
- AI Security Posture Management (AI-SPM)
Cyber Consulting Services
Cybersecurity consulting services provide organisations with expert advice, tools, and strategies to protect their information systems and data from cyber threats.

Cyber Training / Awareness
CYWARIA is our next-generation cyber resilience platform: a cloud-based, real-world cyber wargame. It offers an unmatched, true-to-life platform for cybersecurity teams to train as they would in real incidents, gaining essential real-world experience.
Inspired by actual events, this hyper-realistic training environment simulates lifelike cyber-attacks, blending immersive simulation with gamification.
CYWARIA boasts a vast catalogue of Red and Blue Team exercises of varying lengths and complexities, customised to meet the unique needs of any security team.
Cywareness offers AI Phishing Simulated platform to help organisation enhance their cybersecurity training and cyber awareness.
Crisis Readiness & Management
Digitisation of Crisis Management: Transforming crisis management into a digital platform with essential command and control tools including Communication & Collaboration Tool, Event Log, Crisis Dashboard, Messaging Hub, Strategy Panel, and Risk analysis for comprehensive control and analysis.
Strategic Planning & Training: Prepare playbooks and response strategies based on organisation profile and relevant threat model. This tailored approach, combined with the digital encoding of cyber crises, facilitates precise crisis scoping and efficient data collection according to digital attributes.
Tabletop Exercises: Boost and assess your cyber resilience with our deeply customised and practical tabletop exercises, which simulate real management challenges and genuine cyber threats, offering hands-on experience.
SYGNIA - MILITARY GRADE CYBER SECURITY
Elite Consulting & Incident Response
Industry leading Cybersecurity technologies
We only work with Industry leading Cybersecurity technologies. We do the leg work so you don't have to.
Cybersecurity Knowledge
The team at Witz Cybersecurity has a long history in complex Cybersecurity technologies and IT related security issues.
Consulting Service
We consult with companies to protect their clients' digital systems and DATA from cyber threats.
Continuous Cybersecurity Posture Monitoring
Elite Incident Response & Consulting
Secure All Mobile Devices
Technology Partners
Witz Cybersecurity’s range of unique, disruptive and innovative technologies provides you with the next level of Cyber protection. If you would like a demo or further information, please email us at support@witzcybersecurity.com

Real-time threat detection and response
A comprehensive and customizable cybersecurity platform that provides real-time threat detection and response, deep visibility into an organization's IT environment, and comprehensive vulnerability management solutions.
Detection and Monitoring
Triage and Investigation
Forensic Analysis
Incident Response
Thread Hunting

Trusted Mobile Workplace for Mobile Security
the first endpoint security solution designed to manage mobile data, not mobile devices. Employing the highest levels of data encryption and containerisation – regardless if company owned (COPE) or personally owned (BYOD) – that isolates all work-related email, apps and data from personal use on the same device. No intrusive MDM agents are required.
Single Application Installation
Security without MDM Agents
Zero Trust Endpoint Security
Data Encryption and Containerisation
End-to-End Data Loss Protection (DLP)
Compatible with Both COPE and BYOD



Automated Security Compliance platform
A cloud-native security platform that provides a unified identity and access management solution for cloud-native applications, enabling organizations to secure and control access to their distributed applications and infrastructure.
How Scytale AI reduces the burden of compliance:
Integrations
Automations
Workflows
Compliance Experts
The steps with Scytale AI:
Onboard your company
Add stakeholders
Integrate your tech
Complete tasks
Pass audit
World's first AI Phishing simulator
Introducing the AI Phishing Simulation Builder, a powerful tool that revolutionizes the world of cybersecurity training. With this innovative platform, users can effortlessly generate custom phishing simulations, complete with a phishing email, a convincing phishing landing page, and an insightful micro training.
Cywareness New Features
Improved Export Process: Exporting data is now faster and more efficient! Timestamps have been added to simulation user interactions, streamlining data management.
Enhanced Wizard Power: Empower your training initiatives with our enhanced wizard, now available for both video training and simulations. This feature unlocks new possibilities for your training strategies.
AI Phishing Simulation Builder, a powerful tool that revolutionizes the world of cybersecurity training
Automatic Performance Report: Get analytics of each simulated attack, from opening an email to inserting data into our phishing page.
Cywareness allows you to analyse the performance of each employee, team, department, or even a specific office.

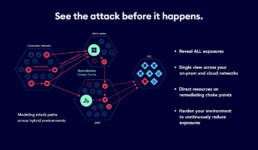
Close today's exposures, prevent tomorrow's attacks
XM Cyber is transforming the way organizations find and fix security exposures across the hybrid cloud. See how attackers leverage and combine misconfigurations, vulnerabilities, identity exposures, and more, across your AWS, Azure, GCP and on-prem environments to compromise your critical assets. With XM Cyber, you can see all the ways attackers might go, and all the best ways to stop them, with a fraction of the effort.
Continuous risk visibility
Safe automated monitoring of entire network
Comprehensive attack modelling from any breach point to critical assets
Proactive security to rapidly prioritize and respond to risk
Hybrid coverage across on-prem and multi- cloud in a single view
Email Security Protection against Cyber-attacks
One of the best email security solutions protecting Government, Law enforcement, legal and financial institutions to name only a few verticals.
Prevention of business email compromise, phishing, and spear-phishing
Neutralization of malicious URLs, attachments, spam and malware
Protection for employees – both in the office and remotely